$285M drained from @DriftProtocol in 12 minutes. April 1st. Not a joke.
Most post-mortems stop at "compromised key." There were two of these in 10 days. Neither happened the way most people imagine.
Here's the actual mechanic ↓
—
➠ One Week Before the Hack: Drift Migrated to a New Multisig
The setup:
▸ 2 of 5 signing threshold
▸ 0-second timelock (instant execution, no delay)
▸ 4 brand-new wallets
▸ 1 carryover signer from the previous structure
That carryover signer was the load-bearing wall.
Five hours before T=0, the carryover signer proposed changing Drift's admin address. One new signer co-signed. Threshold met. No delay.
Admin control transferred instantly.
At that moment, the attacker had full unbounded authority over the entire protocol.
—
➠ They Used It in 12 Minutes
Across 31 transactions, the attacker created a fake spot market for CarbonVote Token (CVT), a worthless token they minted themselves.
They assigned a Switchboard oracle they fully controlled, then pumped it to make 500 million CVT appear worth hundreds of millions in real collateral.
Then raised withdrawal limits 20x across every major market:
▸ $USDC from 25T to 500T
▸ Same for wETH, JLP, dSOL
Every circuit breaker in the protocol, disabled in a single transaction.
—
➠ Then They Drained
JLP vault: 41.7 million to 133 left. 99.9997% gone.
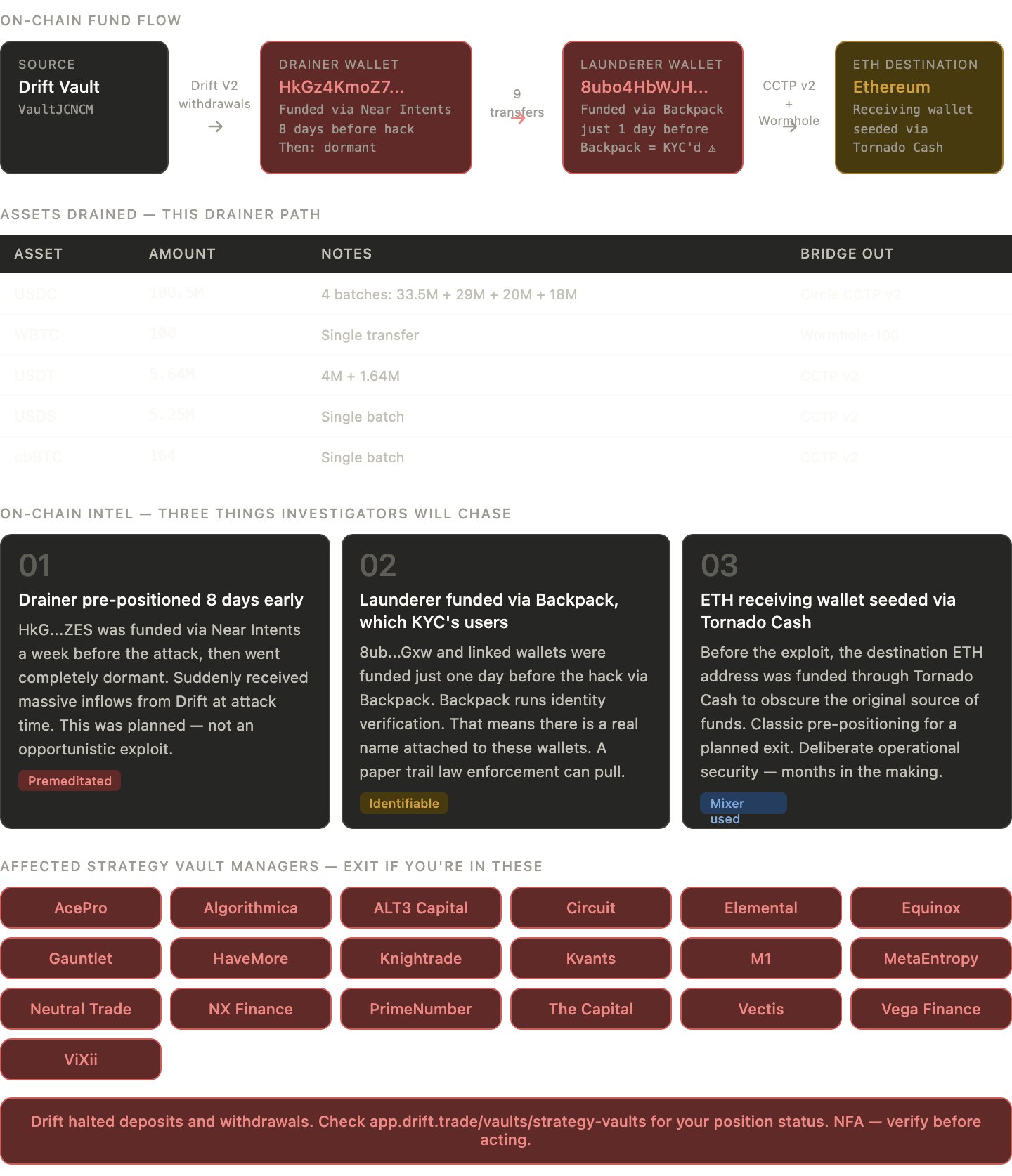
The money path:
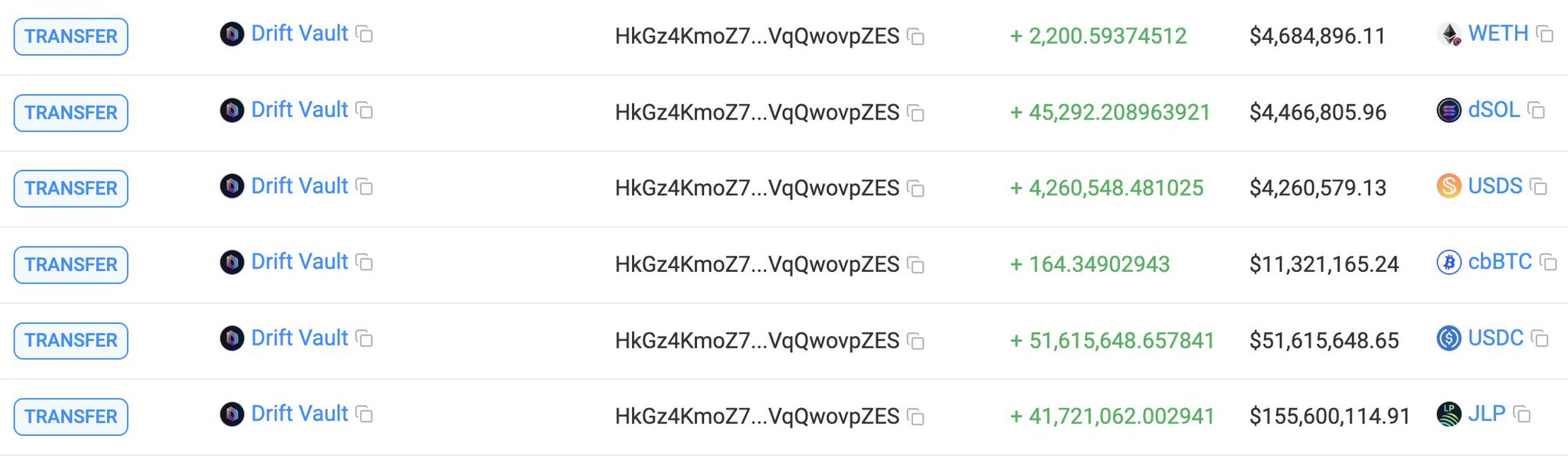
▸ Drift Vault → drainer wallet HkGz4KmoZ7
▸ 9 separate asset transfers → launderer wallet 8ubo4HbWJH
▸ Bridged out to Ethereum via Circle's CCTP v2 and Wormhole
Assets on this single drainer path:
▸ 100.5M USDC across 4 batches
▸ 100 WBTC out via Wormhole
▸ 5.64M USDT
▸ 5.25M USDS
▸ 164 cbBTC
Total protocol drain across all paths: $270M–$285M.
—
➠ Circle took no freeze action.
Despite CCTP being their own bridge. Despite this happening during US business hours. Despite on-chain monitors flagging the exploit in real time. @circle taking no immediate actions.
For context, Circle recently froze 16+ unrelated business wallets but couldn't move on a nine-figure exploit in progress.
Make that make sense.
—
➠ The On-Chain Intel
The drainer wallet (HkG...ZES) was funded via Near Intents 8 days before the hack. Then went completely dormant. No activity at all, until the moment Drift's vaults were hit.
The launderer wallet (8ub...Gxw and linked addresses) was funded just one day before the exploit, via Backpack.
Backpack runs KYC. That means a real name is attached to those wallets. This is the most identifiable thread in the entire operation, and it's a significant opsec failure.
The receiving ETH address was seeded via @TornadoCash before the exploit. The exit route was built weeks or months in advance.
That inconsistency usually points to multiple actors with different levels of operational security. Also the most useful thread for investigators.
—
➠ Compare This to @ResolvLabs
Hit roughly 10 days earlier.
No oracle attack. No fake collateral. A compromised SERVICE_ROLE key used to mint unbacked USR stablecoins directly into the market.
Different execution, identical failure mode: one privileged key, no timelock, no rate limits on what that key could authorize.
Drift: admin key, oracle, fake collateral, drain vaults.
Resolv: service key, mint unbacked tokens, sell.
Both had zero timelocks. Both had admin keys with unbounded authority. Both exposed hundreds of millions in user funds to a single point of failure.
—
➠ If You Have Funds in Any of These Drift Strategy Vaults
Check your position now:
AcePro, Algorithmica, ALT3 Capital, Circuit, Elemental, Equinox, Gauntlet, HaveMore, Knightrade, Kvants, M1, MetaEntropy, Neutral Trade, NX Finance, PrimeNumber, The Capital, Vectis, Vega Finance, ViXii.
Currently, Drift halted deposits and withdrawals.
NFA. DYOR. Stay Safe.