According to Wu, as disclosed by Cyvers Alerts, the $280 million theft from Drift Protocol was a long-term social engineering attack launched by North Korean (DPRK) hackers, not a contract vulnerability. Starting March 23, the attackers set up persistent nonce accounts and compromised the signer, and on April 1, within just a few minutes, exploited the project's 2/5 multi-signature and lack of timelock weakness to gain admin rights and remove withdrawal limits. Currently, Drift has attempted to negotiate via on-chain messages. The ripple effect of this incident has already impacted more than 20 Solana protocols.
https://t.co/hbvl9uYPRy
Wrapped Solana Live Price data
Wrapped Solana SOL Price History USD
Own SOL Now
Buy and sell SOL easily and securely on BitMart.Wrapped Solana X Insight
The Drift hack wasn’t a code exploit.
It was social engineering using Solana’s durable nonces.
Quick explainer on durable nonces ↓
Normally, Solana transactions include a recent blockhash that expires in ~90 seconds. Miss the window and the signed transaction dies.
Durable nonces remove that expiry.
Instead of a blockhash that dies in 90 seconds, you substitute a stored nonce value from a special on chain account. That nonce doesn't expire until someone manually advances it or submits the transaction.
A signed transaction using a durable nonce can sit in someone's pocket for days, weeks, months. Still valid. Still executable. The signer has no visibility into when or whether it gets used.
This exists for good reasons: multisig wallets where signers are in different time zones, cold storage setups, custodial services that need offline signing. But it fundamentally changes the threat model.
How it was weaponized:
- Mar 23: Attacker created four nonce accounts (two tied to Drift security council members
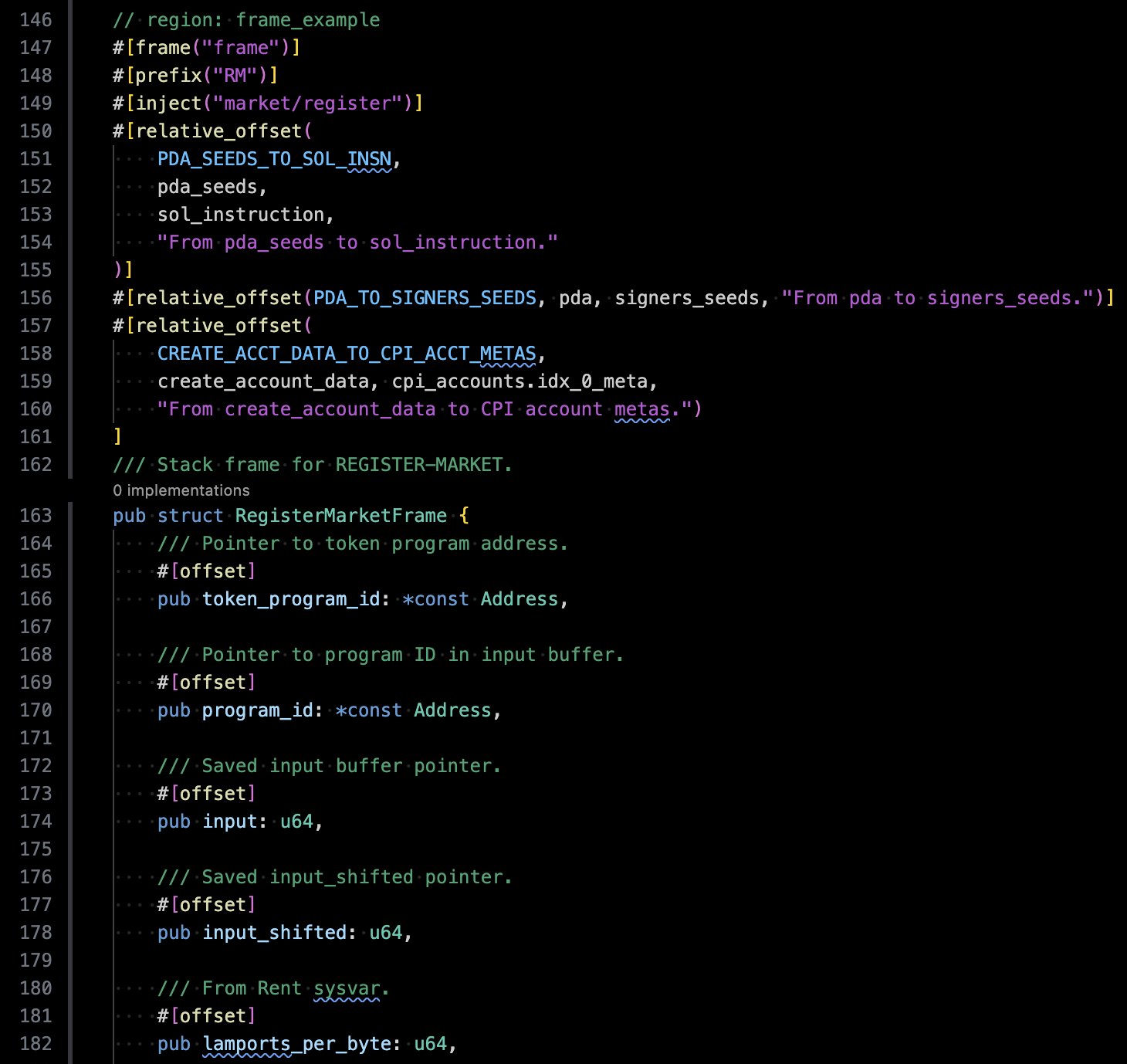
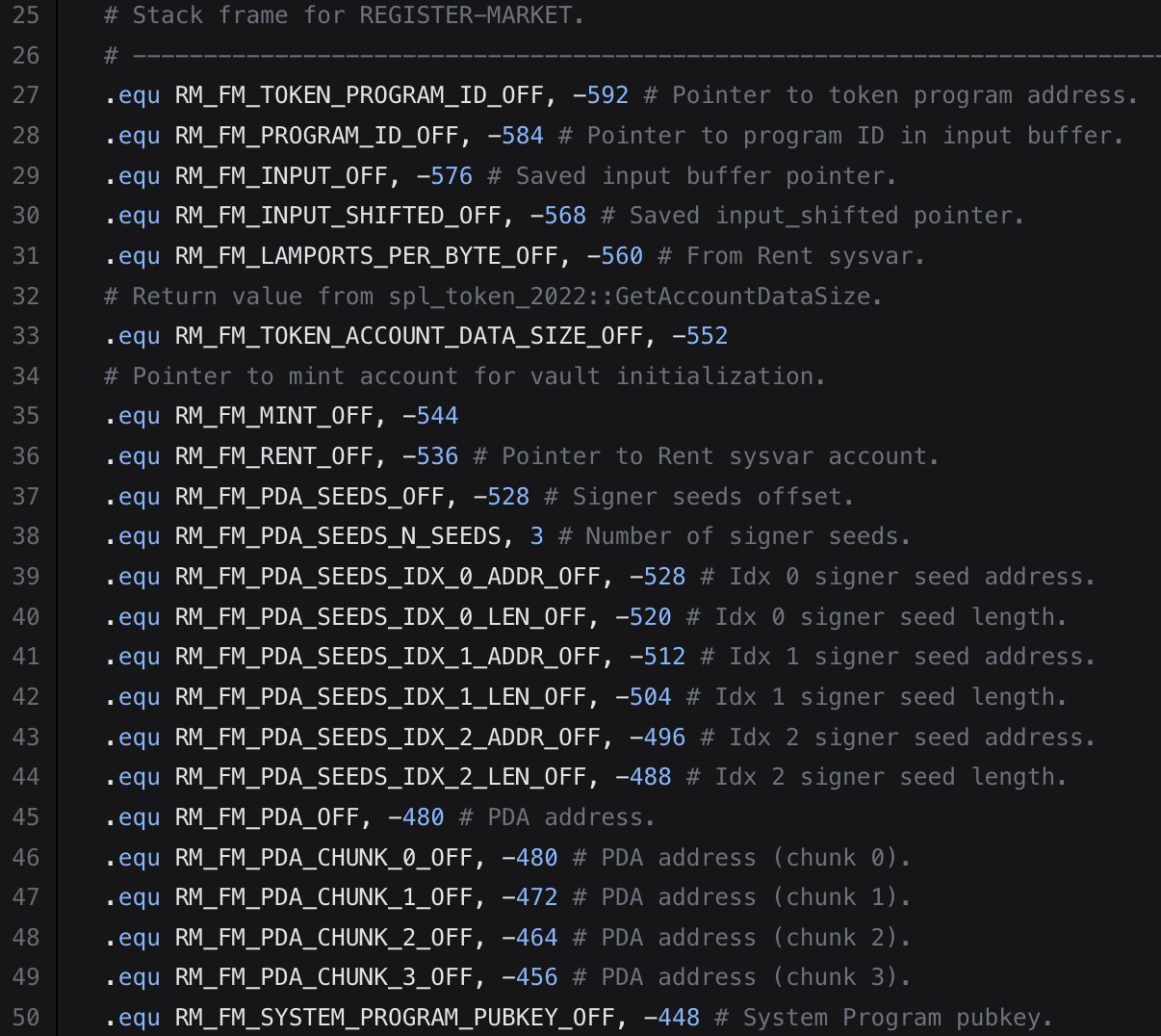
.@Solana SBPF assembly pro tip #21: Declarative frame offset injection
Using the new `#[frame]` struct attribute in Dropset beta (WIP) by @_DASMAC_, you can auto‑inject field offsets via `#[offset]`, `#[signer_seeds]`, `#[sol_instruction]`, and more!
https://t.co/2Gi5TxPMmN https://t.co/OeZ5jI7lyl